CPENT
Certified Testing Professional (CPENT)
Perform effective penetration tests in an enterprise network environment
Phone. +237 673 303 861



Course Description
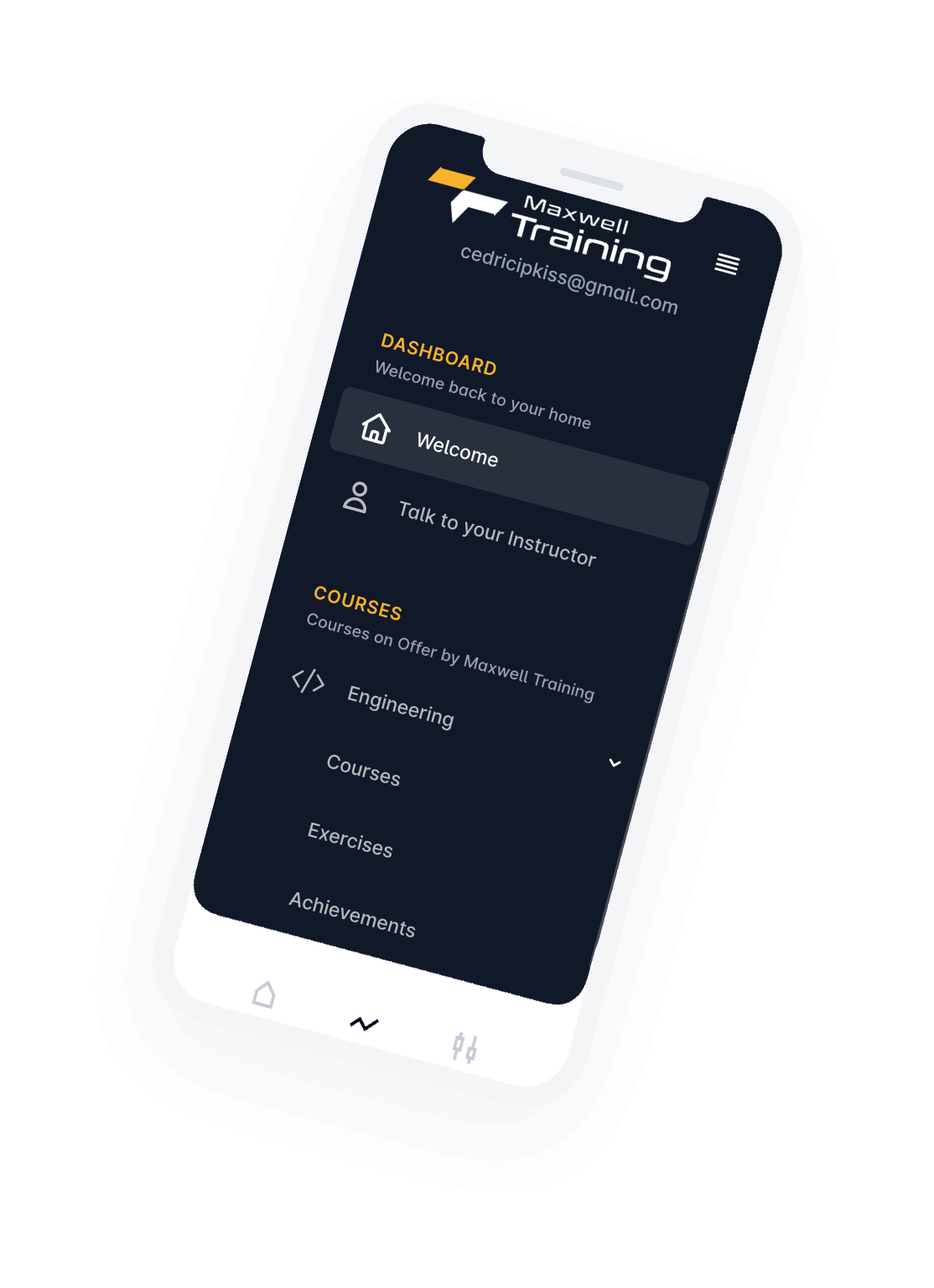
EC-Council’s Certified Penetration Testing Professional (CPENT) program teaches you how to perform an effective penetration test in an enterprise network environment that must be attacked, exploited, evaded, and defended. If you have only been working in flat networks, CPENT’s live practice range will teach you to take your skills to the next level by teaching you how to pen test IoT systems, OT systems, how to write your own exploits, build your own tools, conduct advanced binaries exploitation, double pivot to access hidden networks, and also customize scripts/exploits to get into the innermost segments of the network.
The heart of the CPENT program is all about helping you master your pen testing skills by putting them to use on our live cyber ranges. The CPENT ranges were designed to be dynamic in order to give you a real-world training program, so just as targets and technology continue to change in live networks, both the CPENT practice and exam ranges will mimic this reality as our team of engineers continue to add targets and defenses throughout the CPENT course’s lifetime.
Course Outline

4 Hours Of Praticals
Introduction to Penetration Testing and Methodologies
@Cedric Che-Azeh, @Pousseau Giresse
Cover the fundamentals of penetration testing, including penetration teating approaches, strategies, Methodologies, techniques, and varius guidelines and recommendations for penetration teating

3hours of practicals
Penetration Testing Scoping and Engagement
@Cedric Che-Azeh, @Pousseau Giresse
Learn the different stages and elements of scoping and engagement in penetration testing

5 Hours of Practicals
Open-Source Intelligence(OSINT)
@Cedric Che-Azeh
Learn how to use techniques and tools to gather intelligence about the target from publicity available sources such as the World Wide Web (WWW), through website analysis, by using tools/frameworks/scripts, and so on.

6 Hours Of Praticals
Social Engineering Penetration Testing
@Cedric Che-Azeh
Learn different social engineering techniques and perform social engineering penetration testing on a target organization
8 Hours Of Praticals
Network Penetration Testing-Eternal
@Pousseau Giresse
Learn how to implement a comprehensive Penetration Testing Methodology for assessing networks frrom outsiders' perspective. Learn the process attackers follow to exploit the assets using vulnerabilities from the outside of the network perimeter.
6 Hours Of Praticals
Network Penetration Testing -Internal
@Pousseau Giresse
Learn how to implement a comprehensive penetration testing Methodology for assessing networks from insider's Perspective
4 Hours Of Praticals
Network Penetration Testing-Perimeter Devices
@Pousseau Giresse
Learn How to implement a comprehensive penetration testing Methodology for assessing the security of network perimeter devices, such as Firewalls, IDS Routers, and Switches.

4 Hours Of Praticals
Web Application Penetration Testing
@Cedric Che-Azeh
Learn how to analyze web applications for various vulnerabilitie, including the Open Device Application Security Project (OWASP) Top 10, and determine the risk of exploitation.
5 Hours Of Praticals
Wireless Penetration Testing
@Pousseau Giresse
Learn how to test various components of wireless networks, such as WLAN, RFID devices, and NFC Technology devices

5 Hours Of Praticals
IoT Penetration testing
@Cedric Che-Azeh
Understand various threats to internet of things (IoT) networks and learn how to audit security controls for various inherent IoT risks.

3 Hours of Practicals
OT and SCADA Penetration Testing
@Cedric Che-Azeh
Understand OT and SCADA concepts and learn the process of testing various components of OT and SCADA networks.

4 Hours of Practicals
Cloud Penetration Testing
@Cedric Che-Azeh
Understand various security threats and concerns in cloud computing and learn how to perform cloud penetration testing to determine the probability of exploitation.

3 Hours Of Praticals
Binary Analysis and Exploitation
@Cedric Che-Azeh
Understand the binary analysis Methodology and reverse engineer applications to identify vulnerable applications that may lead to the exploitation of an information system.

3 Hours Of Praticals
Report Writing and Post Testing Actions
@Cedric Che-Azeh, @Pousseau Giresse
Learn how to document and analyze the results of a penetration test and recommend post-penetration test actions.